TLP-WHITE

Walkthroughs, challenges, and examples of host compromises
Introduction
HostIntrusion.com is an educational resource primarily focused on developing skills and knowledge of host based intrusions. These intrusions have been inspired by real-life documented OSINT reports.
Intended audience: SOC analysts, researchers and network defenders - to detect adversary attacks against enterprise IT systems.
Prerequisites: Essential: host and network topologies, infrastructure components/configurations. Basic understanding of Windows and Linux OS, familiarisation of log sources, and knowledge of attack methods is recommended.
License: GNU General Public License v3
Disclaimer: Please handle artifacts with care, and do not use on production systems. Whilst care has been taken to minimise use of malicious artifacts, there could be traces i.e. commands/scripts embedded in logs etc.
Getting Started
The focus of Host Intrusion is primarily on host based artifacts - including logs, and others such as host based agent data and process dumps. There are other artifacts such as network logs (PCAPS and IDS), which provide detailed insights into network behaviour i.e. C2, interactions etc. From a DFIR perspective, disk images and memory captures also provide detailed evidence of host level activity (i.e. user and system). All of these artifacts provide the network defender with a rich insights across both the host and network - however the reality is quite different; i.e. lack of network level monitoring/collection, tool configuration, or lack of skilled personnel.
Audit logs provide a minimum level of security monitoring that can be implemented using vendor best practices. Detection of adversary behaviour using audit logs is largely dependent on the source (i.e. product and configuration), traditionally, audit logs haven’t always provided the low-level signals (i.e. command-line/API interactions etc).
The exercises below aim to walkthrough some of adversary attacks, highlight some of the challenges (gaps) and how other artifacts could be correlated to establish facts and inform conclusions.
Host Intrusion
An host intrusion could be detected by several means, a SIEM alert could be generated in response to an event (i.e. AV alert, configuration change etc), a user could report unusual activity (i.e performance, account lock out etc), or through a pro-active investigation (i.e. hunting for evidence of suspicious activity via IoCs).
The exercises will focus on log sources from a variety of sources, including web servers, domain controllers, sysmon, auditd etc to correlate activity relating to the intrusion, methods of analysis and presenting as part of a incident report.
An APT actor could achieve access via a variety of means. Remote access is traditionally favoured i.e. email, web browser, VPN etc, as opposed to physical or close access i.e. WiFi access, USB drop etc. There are a number of frameworks that can assist the network defender to characterise the stage of the compromise/incident, these include the LockHeed Martin Cyber Kill Chain, MITRE ATT&CK, and Mandiant Attack Lifecycle illustrated below.
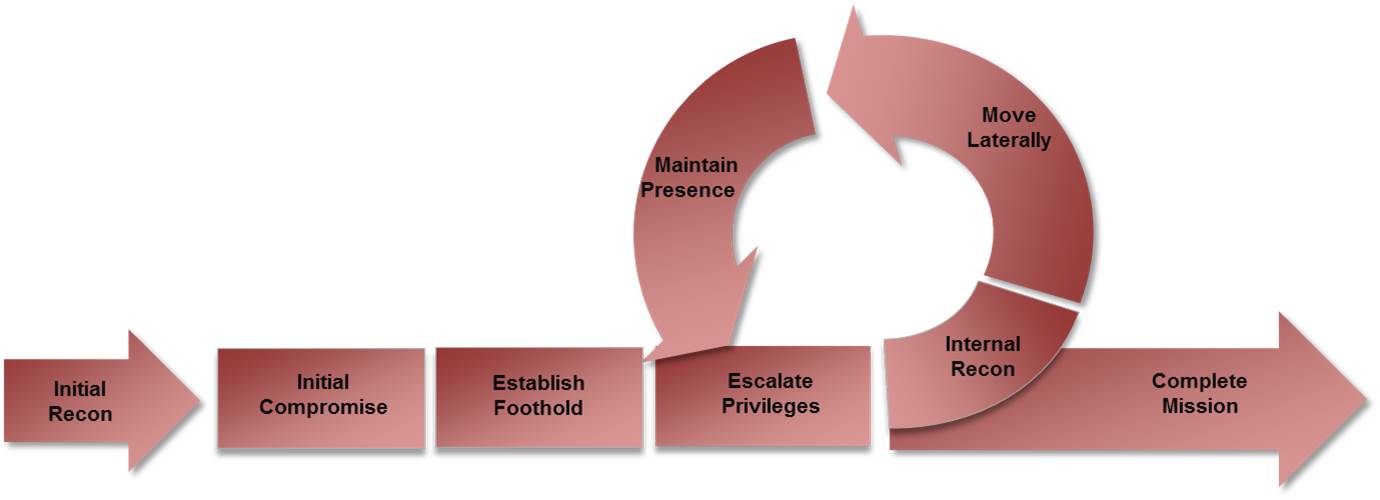
Understanding adversary behaviour is key to understanding how these map to the different stages of the attack lifecycle. The network defender needs to be aware of the tools and techniques that could be used, the methods of detection and how they facilitate the adversary objectives. Cyber threat intelligence sources (reports) play an important role in equipping the network defender with this knowledge.
Methods of detection is typically achieved by using Indicators of Compromise (IoC). At a basic level this could be a hash, file name, IPv4 address etc. The more advanced level of IoC is based on detecting activity, where if the basic level of IoC is changed i.e. hash, the activity will still be detected. Think of this as being an Indicator of Activity (IoA). The pyramid of pain illustrates this concept.
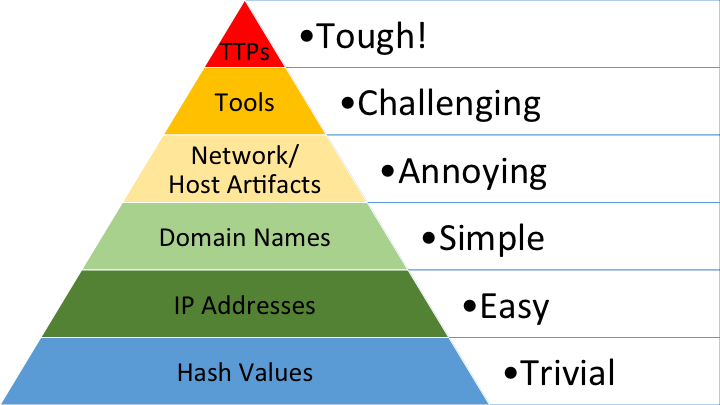 The Pyramid of Pain by David Bianco
The Pyramid of Pain by David Bianco
Exercises
The following exercises aim to walkthrough some scenarios featuring reported attacks (TTPS or tooling). The purpose of these exercises is to expose you to the different types of host artifacts, triage approach and how to determine the host compromise based on available data. Secondly, the exercises have deliberately introduced constraints through improper configuration i.e. logging, clock sync etc, representing real-world challenges.
Tools
A selection of tools for viewing/querying log files via the CLI.
Samples
Link to a Git repo containing a variety of artifacts mapped to MITRE ATT&CK technique IDs. These are small snippets of log entries for example, that are based on known and reported TTPs. Please note, some of these techniques could be dual use i.e. used for legitimate as well as malicious purposes.
Good Practices
Authority resources that provide good practices from host configuration through to incident response.
- NIST Guide to Computer Security Log Management
- NCSC Introduction to Logging
- NCSC Logging Made Easy
- ACSC Windows Event Logging and Forwarding
Recommended Books
- Counter Hack Reloaded by Ed Skoudis
- Malware - Fighting Malicious Code by Ed Skoudis
- The Art of Memory Forensics by Michael Hale Ligh, Andrew Case, Jamie Levy, AAron Walters
- Real Digital Forensics: Computer Security and Incident Response by Keith J. Jones, Richard Bejtlich
References
Curated list of references grouped by theme, a mix of primer, look-ups, configurations and vendor recommendations.
Primer
Microsoft Windows
- Microsoft - Events to Monitor
- NSA - Recommended Events to Collect
- Windows EVTX Samples
- UltimateWindowsSecurity - EventID Lookup
- Microsoft - Event Logs
- SANS - Event IDS
Linux
Configuration
Threat
- Mitre ATT&CK Enterprise Matrix
- ActiveCountermeasures - Log Analysis
- UK Home Office Cyber - Detecting the Unknown
- Mandiant - Anatomy of an APT
- Lockheed Cyber Kill Chain
- Elastic Threat Hunting Guide
What Next?
- To develop your own lab to generate/test artifacts, to understand logging configuration, then the NCSC Logging Made Easy provides a purpose built solution based on the Elastic platform. Instructions are available on the NCSC GitHub: LME.
- Understanding detection rules. Elastic has made available a number of rules via their GitHub: Elastic/Detection-rules